עגלה למכונת כביסה/מייבש | עגלות מטבח | ארגון וטקסטיל למטבח | מטבח, אירוח וחד פעמי | הקניון הכל לבית | קטגוריות | Shufersal

עגלה למכונת כביסה/מייבש | עגלות מטבח | ארגון וטקסטיל למטבח | מטבח, אירוח וחד פעמי | הקניון הכל לבית | קטגוריות | Shufersal

הום סנטר Home Center - מבצע ליומיים בלבד ורק לרוכשים באתר הום סנטר! מכונת כביסה BOSCH קיבולת 7 ק״ג כולל אחריות יבואן רשמי ב-1,299 ש״ח כולל הובלה עד הבית 😱 >>> https://bit.ly/3ffzmyH

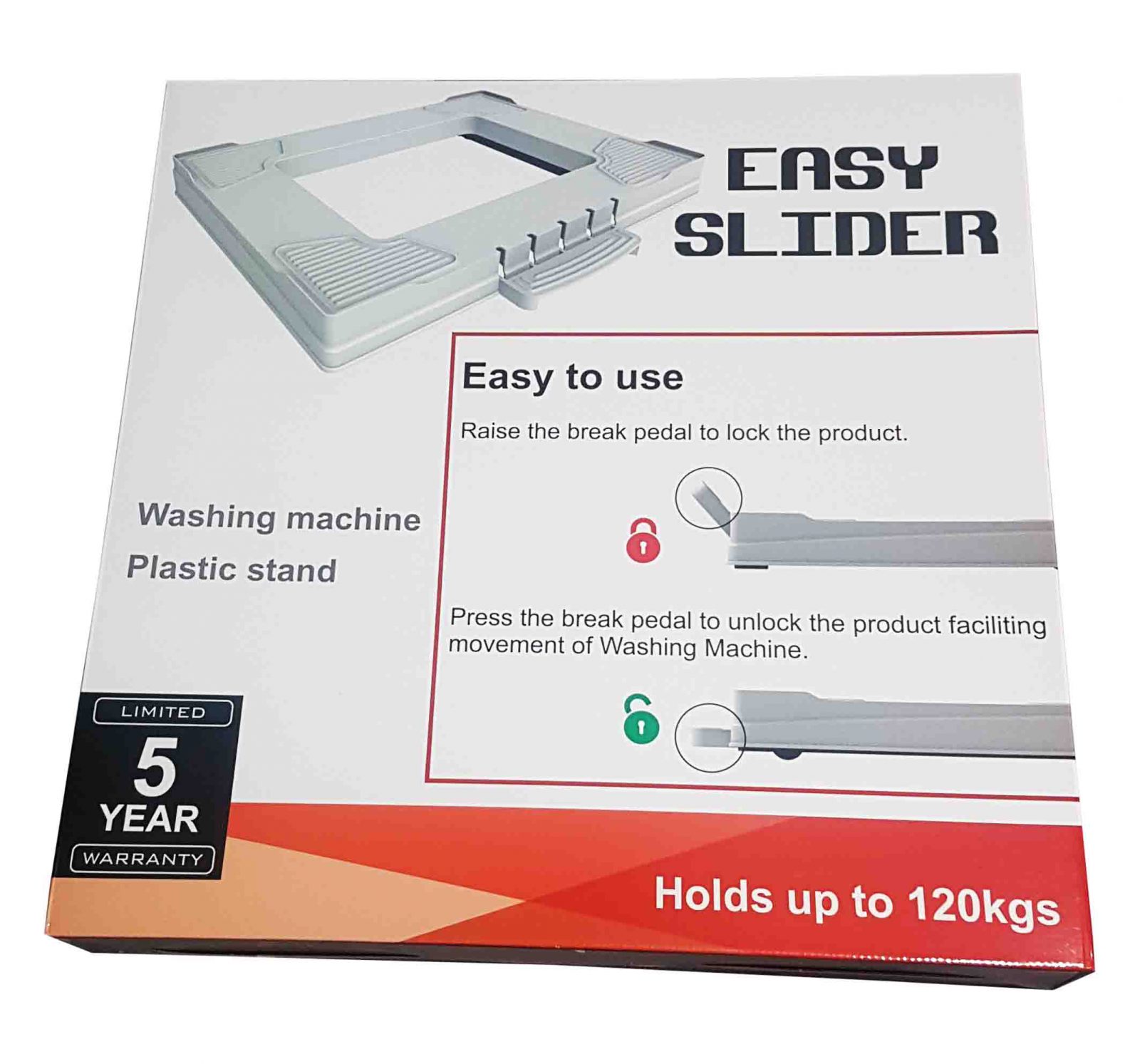
Easy Slider - איזי סליידר - רק 199 ש"ח ועגלה אצלך !! עגלת הרמה למכונות כביסה המשמשת גם כעגלה למכשירי חשמל גדולים. העגלה מתאימה לכל סוגי וגדלי מכונות הכביסה הפופולאריות ומספקת מענה